Supply Chain Traceability for Anti Counterfeiting
Combating Counterfeiting Through Data Analysis
Understanding the Scope of Counterfeiting
Counterfeiting is a pervasive global issue, impacting various industries and economies. It's not just a matter of consumer deception; counterfeit products often pose significant safety risks, undermining brand reputation, and eroding trust in legitimate businesses. The sheer scale of this problem necessitates innovative solutions, and data analysis plays a crucial role in identifying, tracking, and ultimately combating these fraudulent activities.
The ramifications extend far beyond the immediate sale of a counterfeit product. It affects consumer health and safety, potentially leading to serious consequences from faulty materials to outright hazardous components. Furthermore, the economic impact of counterfeiting is substantial, costing legitimate businesses billions in lost revenue and market share.
Identifying Counterfeit Products through Pattern Recognition
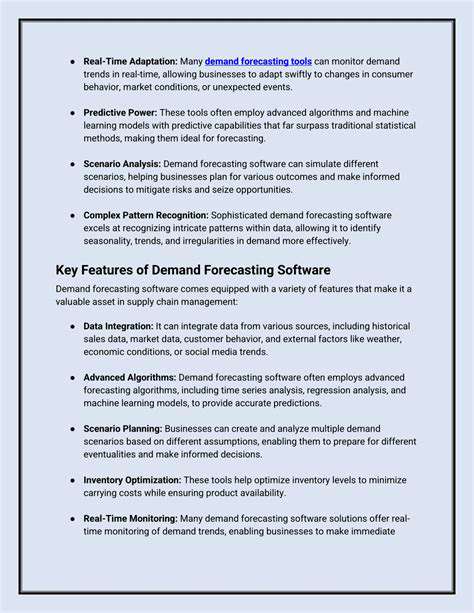
Data analysis offers powerful tools for identifying patterns that suggest counterfeiting. By analyzing vast datasets of product information, including origin, manufacturing processes, and distribution channels, sophisticated algorithms can pinpoint anomalies and inconsistencies that may indicate fraudulent activities. This involves scrutinizing every aspect of the supply chain, from raw materials to finished products, to detect deviations from established norms.
Advanced data visualization techniques can highlight these anomalies, allowing analysts to quickly identify potential counterfeits. Through machine learning, these systems can learn from past cases and become increasingly adept at recognizing and predicting fraudulent patterns.
Leveraging Blockchain Technology for Transparency
Blockchain technology, with its immutable and transparent nature, is a game-changer in combating counterfeiting. By recording every step in a product's journey on a shared, decentralized ledger, blockchain creates an auditable trail that can verify authenticity. This transparency significantly reduces the possibility of tampering or alteration throughout the supply chain.
This detailed record, accessible to all authorized parties, enhances consumer confidence and allows businesses to swiftly trace the source of counterfeit products. The use of blockchain provides a robust defense against counterfeiting, and it offers a reliable mechanism for consumers to verify the legitimacy of products.
Analyzing Consumer Data to Predict Demand and Counterfeit Trends
Analyzing consumer data offers insights into purchasing patterns and preferences. This information can be used to predict potential demand for certain products, which can help anticipate counterfeit activity. By understanding consumer behavior and market trends, businesses can proactively adjust their strategies to mitigate the risks associated with counterfeit products.
This forward-looking approach is essential for maintaining a strong market position and protecting against fraudulent activities. Identifying potential demand fluctuations and associated counterfeit risks allows for more effective resource allocation and strategic planning.
Implementing Data-Driven Supply Chain Security Measures
Data analysis allows for the implementation of data-driven supply chain security measures. By identifying vulnerabilities in the supply chain, businesses can implement protective measures and enhance their security protocols. This proactive approach involves strengthening security at each stage of the production and distribution process.
These measures can involve implementing advanced tracking systems, employing more stringent authentication procedures, and establishing stronger relationships with trusted suppliers and distributors. Ultimately, these strategies contribute to building a more resilient and secure supply chain.
Improving Product Authentication and Verification Processes
Data analysis plays a vital role in improving product authentication and verification processes. By incorporating data-driven insights into existing systems, businesses can create more efficient and accurate methods for verifying product authenticity. This includes using unique identifiers, embedded microchips, or other advanced technologies to ensure products are legitimate.
Implementing digital verification tools and processes that consumers can access and use directly provides a robust and transparent means of product authentication. This approach builds consumer trust and helps to establish a more secure and reliable marketplace.
Enhancing Collaboration and Information Sharing
Combating counterfeiting effectively requires strong collaboration among stakeholders. Data analysis can facilitate this collaboration by enabling the sharing of information and insights across the supply chain. This includes sharing data on counterfeit trends, product authentication methods, and best practices for security.
The development of industry-wide protocols and data-sharing platforms provides a shared understanding of the counterfeiting landscape and allows stakeholders to work together to effectively combat this pervasive issue. This collective effort significantly strengthens the overall anti-counterfeiting strategy.
The Future of Anti-Counterfeiting Through Traceability
Enhanced Product Authentication
Anti-counterfeiting efforts are increasingly focusing on enhanced product authentication, moving beyond simple labels and holograms. This involves integrating sophisticated technologies like blockchain, RFID tags, and unique serial numbers into the supply chain, creating a verifiable digital record of a product's journey from origin to consumer. This digital trail allows consumers to instantly verify the authenticity of a product, making it far more challenging for counterfeiters to replicate.
By embedding these technologies into packaging and product components, businesses can create a robust authentication system, deterring counterfeiters and ensuring consumers receive genuine goods. This proactive approach to authentication fosters trust and strengthens brand reputation, ultimately benefiting both the manufacturer and the end-user.
Improved Supply Chain Transparency
Traceability systems provide unprecedented visibility into the entire supply chain, from raw materials to finished goods. This increased transparency allows businesses to identify potential vulnerabilities and address them quickly, mitigating risks associated with counterfeiting and other supply chain disruptions. Real-time monitoring of product movement through the supply chain enables swift identification of discrepancies and allows for proactive intervention.
By knowing exactly where each component or product is at any given time, manufacturers can more efficiently manage their inventory, reduce waste, and enhance overall supply chain efficiency. This transparency also builds trust with consumers, who can feel confident that the products they purchase are authentic and ethically sourced.
Technological Advancements in Tracking
The future of anti-counterfeiting relies heavily on advancements in tracking technologies. Innovations like advanced barcodes, near-field communication (NFC) tags, and sensor integration are transforming how products are monitored and authenticated. These technologies provide a more comprehensive and secure way to track the movement of goods, reducing vulnerabilities and increasing the speed of response to potential counterfeiting issues.
Protecting Intellectual Property
Traceability systems play a crucial role in safeguarding intellectual property rights. By creating a clear and verifiable record of a product's journey, companies can more effectively identify and prosecute counterfeiters. This detailed record of origin and manufacturing processes acts as a powerful deterrent, making it more difficult for counterfeiters to replicate products and bypass legal protections. This comprehensive tracking system strengthens brand protection, ensuring that consumers are not misled and that the legal rights of manufacturers are upheld.
Furthermore, this robust tracking system can help brands build a stronger case for legal action against counterfeiters. The detailed records of a product's journey provide evidence to support legal claims and strengthen the ability to recover damages and prevent further counterfeiting activity.
Consumer Empowerment and Trust Building
The ultimate goal of anti-counterfeiting through traceability is to empower consumers and build trust in the supply chain. By providing consumers with easy access to product authenticity information, traceability systems foster trust and build confidence in the products they purchase. This empowers consumers to make informed decisions and contributes to a more transparent and secure market.
Consumers can easily verify the authenticity of a product via a mobile app or online platform, providing them with the tools to avoid counterfeit goods. This level of transparency reinforces the importance of ethical sourcing and promotes responsible consumption, ultimately benefiting both consumers and businesses alike.
Read more about Supply Chain Traceability for Anti Counterfeiting
Hot Recommendations
- AI for dynamic inventory rebalancing across locations
- Visibility for Cold Chain Management: Ensuring Product Integrity
- The Impact of AR/VR in Supply Chain Training and Simulation
- Natural Language Processing (NLP) for Supply Chain Communication and Documentation
- Risk Assessment: AI & Data Analytics for Supply Chain Vulnerability Identification
- Digital twin for simulating environmental impacts of transportation modes
- AI Powered Autonomous Mobile Robots: Enabling Smarter Warehouses
- Personalizing Logistics: How Supply Chain Technology Enhances Customer Experience
- Computer vision for optimizing packing efficiency
- Predictive analytics: Anticipating disruptions before they hit